The modern hospital is no longer just a facility of medicine; it is a sprawling, interconnected data center where patient outcomes are inextricably linked to network uptime. At US Healthcare Today, we have observed a dangerous divergence: while clinical technology has leaped forward, the security infrastructure supporting it remains trapped in a state of perpetual vulnerability. The Internet of Medical Things (IoMT): ranging from smart infusion pumps to high-definition imaging systems: has become the soft underbelly of the healthcare sector.
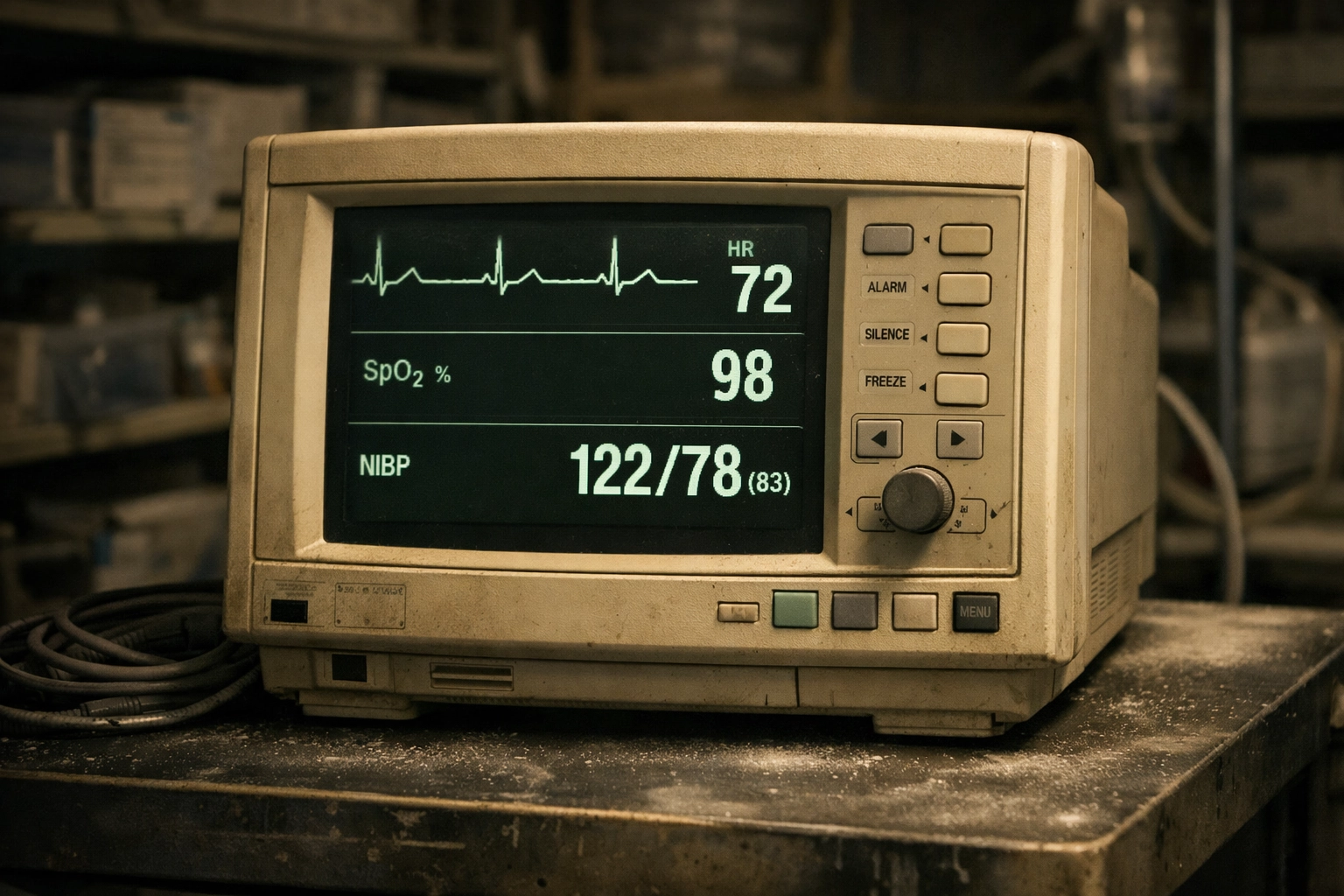
We are witnessing a crisis where medical devices are treated as clinical assets first and IT liabilities second. This hierarchy of priorities, while understandable in a life-saving context, is exactly what ransomware groups exploit. When a ventilator or a heart monitor is compromised, it isn't just a data breach; it is a direct threat to patient safety. The reality is stark: many hospitals are unknowingly laying out the red carpet for cybercriminals by making fundamental errors in how they deploy and manage their IoMT fleets.
The Default Credential Crisis: Leaving the Front Door Unlocked
One of the most egregious mistakes we see in current hospital environments is the persistence of default or weak credentials. Research indicates that approximately 21% of medical devices in active use today rely on default passwords that are publicly available in manufacturer manuals. Even more alarming is the fact that nearly 9 out of 10 devices ship from the factory with these "out-of-the-box" credentials.
In many clinical settings, the priority is "ease of access." A nurse or technician needs to interact with a device immediately, and a complex password protocol is often viewed as a barrier to care. However, we must be clear: an easily accessible device for a clinician is an easily accessible entry point for an attacker. Once a ransomware group gains access to a single device using a default password, they can move laterally across the network, escalating privileges until they control the hospital’s entire digital infrastructure.
Nursing the Undead: The Persistence of Legacy Systems
We must address the "zombie" hardware haunting hospital corridors. Approximately 60% of medical devices currently in use are considered end-of-life (EOL), meaning the manufacturers no longer provide security patches or technical support. Furthermore, about 14% of the IoMT ecosystem is still running on archaic operating systems like Windows XP or Vista.
From a clinical utility standpoint, these machines might still function perfectly. A ten-year-old MRI machine still produces high-quality scans. However, from a cybersecurity perspective, these devices are "ransomware bait." They lack the modern architecture required to defend against sophisticated botnets and encryption scripts. When a device cannot be patched, it becomes a permanent vulnerability. At US Healthcare Today, we frequently cover these risks in our news analysis section, highlighting how legacy hardware often serves as the patient zero for large-scale hospital shutdowns.
The Fatal Flaw of the Flat Network
Perhaps the most structural mistake hospital IT leaders make is maintaining a "flat" network architecture. In a flat network, there is no meaningful separation between a visitor’s smartphone on the guest Wi-Fi, a workstation in the billing department, and an infusion pump in the Intensive Care Unit.
If we do not segment these devices into isolated micro-networks, we are essentially building a house where every room is connected by an open hallway with no doors. If an attacker compromises a non-critical device: perhaps a smart thermostat or a digital signage board: they have a direct path to the hospital’s most sensitive clinical systems. Ransomware thrives in flat environments because it can spread unchecked, encrypting everything in its path before the IT team even receives an alert. Effective IoMT security requires rigorous network segmentation, ensuring that clinical devices only communicate with the specific servers and systems necessary for their function.
The "Vendor Fallacy": Assuming Out-of-the-Box Security
There is a pervasive and dangerous myth among hospital administrators that if a device is FDA-cleared and purchased from a reputable medical vendor, it is inherently secure. We must debunk this assumption. While vendors are responsible for the clinical efficacy and initial safety of the device, the ongoing security of that device once it sits on a hospital network is a shared responsibility.
Too often, hospitals skip updates or lack visibility into the patch status of their equipment, assuming the vendor is managing it remotely. Conversely, some vendors provide patches that are never implemented because the hospital fears that an update might cause downtime or void a warranty. This "responsibility gap" is where ransomware thrives. We believe it is imperative for healthcare organizations to move toward a model of active verification. Do not assume the device is safe; prove it is safe through continuous monitoring and rigorous auditing.
Encryption Gaps and Unsecured Transmissions
In our deep dives into AI and digital health, we often find that the "intelligence" of these devices outpaces their security protocols. Many IoMT devices communicate over wireless networks using unencrypted or poorly secured protocols. This makes them vulnerable to man-in-the-middle attacks, where an actor can intercept data or inject malicious commands.
Inadequate encryption isn't just a HIPAA violation; it’s a functional risk. If an attacker can intercept the communication between an infusion pump and its management server, they can potentially alter dosage instructions or disable the device entirely. When devices are "chatty" on the network without encryption, they provide a roadmap for attackers to understand the hospital's internal logic, making it easier to craft a devastating ransomware payload.

The Patch Management Paradox
The sheer volume of vulnerabilities facing healthcare is staggering. With over 211,890 distinct vulnerabilities currently identified and 2,500 new ones emerging every month, IT departments are often paralyzed by the scale of the task. For resource-constrained hospitals, keeping up with firmware updates for thousands of individual devices is an impossible manual task.
This leads to "patch fatigue," where critical security updates are deferred in favor of more immediate operational needs. Ransomware attackers are acutely aware of this lag time. They often weaponize "N-day" vulnerabilities: flaws that have been publicly disclosed and patched by the vendor but remain unaddressed on the hospital’s devices. To bridge this gap, we recommend that IT leaders invest in automated IoMT discovery and security platforms that can provide real-time visibility into the patch status of every connected asset.
Why Hospitals are the Ultimate Target
We must understand the psychology of the attacker to defend against them. Medical devices are uniquely attractive for ransomware because, unlike a corporate laptop, they cannot simply be wiped and restored while the business continues. If a patient’s life depends on a connected monitor, the hospital faces extreme, life-and-death pressure to restore functionality immediately.
Cybercriminals know that the cost of downtime in healthcare is measured in human lives, not just dollars. This makes hospitals more likely to pay a ransom to regain control of their clinical systems. By leaving medical devices unpatched, unsegmented, and secured with default passwords, hospitals are essentially subsidizing the very criminal organizations that target them.
A Path Forward for Hospital Leadership
Addressing the IoMT security gap requires a shift in organizational culture. We suggest the following immediate actions for hospital administrators and IT leaders:
- Inventory Everything: You cannot protect what you cannot see. Conduct a comprehensive audit of every connected device on your network, including its OS version and patch status.
- Enforce Segmentation: Isolate IoMT devices from the rest of the IT network. Clinical traffic should never mingle with general administrative or guest traffic.
- Audit Credentials: Mandate a "no default password" policy. If a device does not allow for credential customization, it should be placed behind a rigorous hardware firewall.
- Hold Vendors Accountable: Before purchasing new equipment, demand a detailed Software Bill of Materials (SBOM) and a clear commitment to long-term security patching.
- Bridge the Gap: Create a collaborative task force between clinical engineering (Biomed) and IT security. These two departments must speak the same language to protect the hospital effectively.
The era of viewing medical devices as isolated tools is over. They are nodes on a hostile network, and they must be defended with the same vigor as the electronic health record itself. At US Healthcare Today, we remain committed to exposing these vulnerabilities and advocating for a healthcare system that is as secure as it is innovative. The safety of your patients now depends as much on your firewall as it does on your physicians.



Leave a Reply